Management
OPM guidance details when agencies can ask about applicants' criminal history
Though the federal government had already implemented a form of “ban the box” administratively, the Fair Chance to Compete for Jobs Act necessitated an update of the policy.
Pay & Benefits
Postponing retirement problems: Part 2
Federal law trumps what might seem to make the most sense.
Management
House panel advances bill to make federal contracting easier to understand
The Plain Language in Contracting Act would require agencies to use easy-to-understand language for certain procurement notices pertaining to small businesses.
Management
Senators call on postal board to abandon DeJoy’s USPS reforms
The overhaul is harming the Postal Service, Democrats say, though postal leadership says it just needs more time.
Sponsor Content
GovExec TV: Five Questions with Kurt Steege
Oversight
New bill would establish an IG for the Supreme Court
The Judicial Ethics Enforcement Act calls for a new inspector general’s office to investigate alleged misconduct and prevent waste, fraud and abuse across the judicial branch.
Workforce
Can Biden’s new jobs program to fight climate change attract women and people of color?
The American Climate Corps program aims to recruit a diverse workforce. But it will face challenges including low pay, the need for child care, and historic discrimination against women in the trades.
Management
Bipartisan group looks to push IRS towards simpler math error notices
The IRS MATH Act would require the tax agency to send more specific, straightforward notices when it corrects simple math errors on tax returns.
Sponsor Content
Innovate with Lumen for public administration agencies
Take advantage of the full range of capabilities needed for success in a digital-first business landscape, delivered in a simple platform approach.
Pay & Benefits
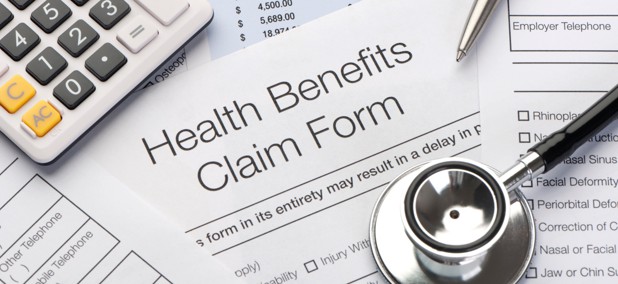
Are High Deductible Health Plans the right FEHB plan for you?
For most federal employees, HDHPs will be the cheapest FEHB plan type. Here’s how they work.
FEATURED INSIGHTS
Workforce
VA employee discipline back in the spotlight as lawmakers move new bills
Another measure would provide VA managers with more training on disciplining employees.
Pay & Benefits
Congressional Dems urge OPM to fully cover IVF in feds’ insurance program
More than 175 Democratic lawmakers said the federal government must do more to protect access to health services like in-vitro fertilization in light of a recent Alabama court ruling that effectively banned the procedure alongside abortion services.
Tech
Federal CIO defends Login security after health agency dropped it from grantee system
Clare Martorana doubled down on Login’s capabilities, saying the government “needs to continue to rely” on the tool.
TSP TICKER
FUND
G
F
C
S
I
APR 24 CLOSE
$18.2032
$18.6378
$79.4041
$78.0805
$41.4796
DAILY CHANGE
0.0022
-0.0454
0.0175
-0.1427
-0.0426
THIS MONTH (%)
0.28
-2.32
-3.41
-5.28
-2.57
FUND
L 2060
L 2050
L 2040
L 2030
L INCOME
APR 24 CLOSE
$15.8374
$31.7868
$53.0138
$46.6852
$25.4040
DAILY CHANGE
-0.0079
-0.0181
-0.0264
-0.0184
-0.0045
THIS MONTH (%)
-3.35
-2.89
-2.52
-2.06
-0.80
FUND
APR 24
CLOSE
CLOSE
DAILY
CHANGE
CHANGE
THIS
MONTH
MONTH
G
$18.2032
0.0022
0.28
F
$18.6378
-0.0454
-2.32
C
$79.4041
0.0175
-3.41
S
$78.0805
-0.1427
-5.28
I
$41.4796
-0.0426
-2.57
L 2050
$31.7868
-0.0181
-2.89
L 2040
$53.0138
-0.0264
-2.52
L 2030
$46.6852
-0.0184
-2.06
L 2020
$None
None
L INCOME
$25.4040
-0.0045
-0.80
Management
New rule cements sustainability mandate for federal buyers
A new update to the Federal Acquisition Regulation is meant to help the government meet goals for net-zero procurement by 2050.
Management
Biden signs extension of controversial spying program into 2026
The Section 702 authorities were reauthorized without the addition of a warrant requirement to review the communications of Americans caught up in foreign surveillance.
Workforce
State, Defense departments announce deal to expand military spouse access to remote work jobs
The move to allow federal employees to telework while overseas with their service member spouses is part of a larger effort to boost recruitment of military spouses.
Workforce
Biden announces first tranche of Climate Corps jobs with hopes of segueing thousands into federal service
Participants can leverage their experience into federal internships and jobs.
Management
GSA lacks management controls for keeping foreign gifts, IG says
An inspector general’s audit of the agency’s Foreign Gifts and Decorations Program found that GSA officials were missing gifts from its inventory while also possessing prohibited items due to insufficient management practices.
Management
FEMA is making an example of this Florida boomtown. Locals call it ‘revenge politics’
The Biden administration is trying to punish Lee County for rebuilding flood-prone homes. The state’s Republican politicians are fighting back.
Management
Senate Veterans’ Affairs chair calls for more mental health care providers in rural areas
Sen. Jon Tester, D-Mont., asked VA Secretary Denis McDonough to increase the number of providers and ensure they are “in locations where veterans need them most.”
Management
BLM to finalize rule allowing federal leases targeted at protection of natural areas
The rule marks a shift in the agency’s focus toward conservation.
Management
Biden administration to roll back the Betsy DeVos Title IX rules
New Education Department regulations would undo Trump administration changes to sexual discrimination policies at U.S. colleges and universities, now requiring the schools to have in place measures to offer support to students and employees alleging discrimination.
Pay & Benefits
OPM has new tools to fight improper health insurance enrollments
Watchdog agencies and Congress have previously chided the federal government’s HR agency for the lack of internal controls ensuring that family members of federal workers and retirees remain eligible for the federal workforce’s health insurance program.
Pay & Benefits
Justice Department outlines benefits rule for Havana syndrome victims
A new interim final rule details how the department would compensate employees and dependents with qualifying brain injuries from anomalous health incidents.
Management